News
Have you been avoiding confronting a troublesome colleague, disagreeing with your partner, or asking your boss for a raise? If there was a way to have difficult conversations easily, what would that do for you? We avoid difficult conversations out of fear that we will make things worse. We are often worried about how we […]
Do you want to be a powerful influencer? Do you want to make more friends, double your sales, and get through to people easily? Discover proven ways to ethically program peoples’ unconscious minds and gain compliance 10x faster. Master Persuasion and Influence is a comprehensive course based on the work of renowned hypnotists, therapists, and […]
This course is designed to teach you how to build a video classification model using Keras and TensorFlow, with a focus on action recognition. Video classification has numerous applications, from surveillance to entertainment, making it an essential skill in today’s data-driven world. Through this course, you will learn how to extract features from video frames […]
In today’s digital age, video marketing is a critical component of any successful marketing strategy. If you’re looking to effectively promote your business, engage with your audience, and drive sales, you need to have a solid understanding of video and YouTube marketing. At Zahavi Digital, we offer a comprehensive course on video and YouTube marketing […]
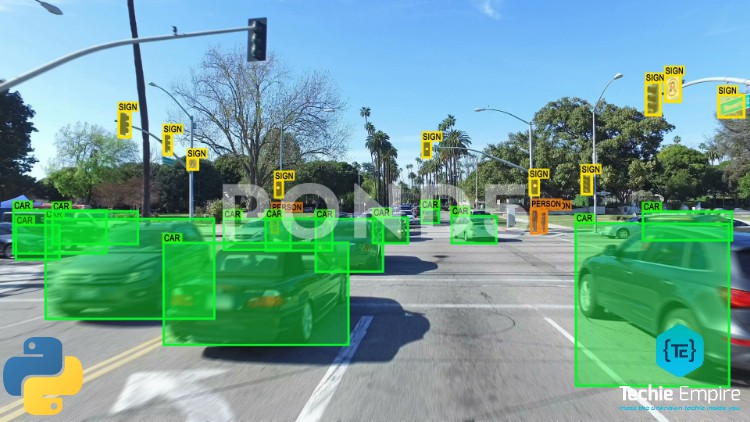
Detecting Objects and finding out their names from images is a very challenging and interesting field of Computer Vision. The core science behind Self Driving Cars, Image Captioning and Robotics lies in Object Detection. In this course, you are going to build a Object Detection Model from Scratch using Python’s OpenCV library using Pre-Trained Coco […]
A vulnerability is a flaw that could lead to the compromise of the confidentiality, integrity or availability of an information system. Vulnerability identification involves the process of discovering vulnerabilities and documenting these into an inventory within the target environment. Over the years, security researchers and vendors have sought to make the process of vulnerability identification […]
As technology continues to become more relevant for businesses worldwide, the importance of securing business-critical applications and their underlying tech stack continues to gain prominence. With the changing threat landscape, it is often impractical to identify vulnerabilities in real time by simply leveraging automated tools. To help with this, Ethical Hacking has been steadily gaining […]
What is Python 2? Python 2 made code development process easier than earlier versions. It implemented technical details of Python Enhancement Proposal (PEP). Python 2.7 (last version in 2.x ) is no longer under development and in 2020 will be discontinued. Although, Python 2 is an old open source version here are where you still […]
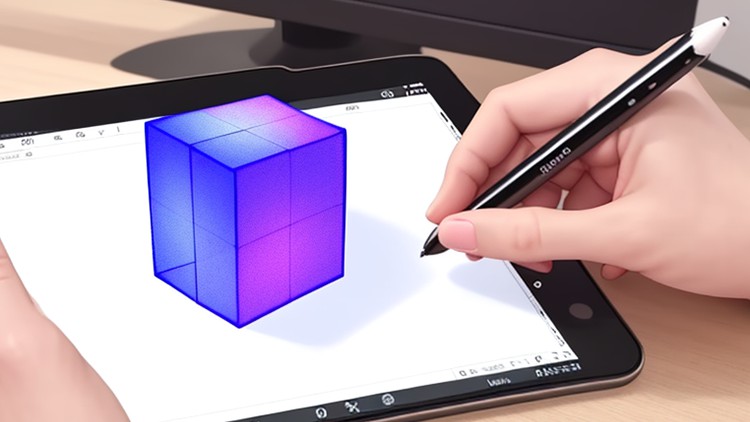
Are you an artist or designer looking to bring your paper sketches to life in a whole new way? In this course, you’ll learn how to turn your sketches into interactive art pieces using Unity, Augmented Reality, and Vuforia. Throughout the course, you’ll work on multiple projects, from sketching a character to creating an AR […]
Everyone has been hurt in one way or another. Few people are able to let that pain go so they can move on with their lives without the past interfering with their joy. People have a tendency to get caught in their anger and pain after they’ve been hurt. There are mental, emotional, and physical […]