News
I always wanted to learn the fundamentals of web development. I’m drawn to how easy and quickly one can create visuals to be displayed within a web browser. Coming from a background in Python where the vast majority of my learning took place in a terminal, web development seemed so enticing! However, there was one […]
We will use msfvenom for creating a payload and save it as an apk file. After generating the payload, we need to setup a listener to Metasploit framework. Once the target downloads and installs the malicious apk then, an attacker can easily get back a meterpreter session on Metasploit. An attacker needs to do some […]
This course provides an introduction to the fundamentals of quantity surveying for civil works projects with a focus on using PlanSwift software for quantity takeoff and measurement. Students will learn how to interpret construction drawings, extract quantities and measurements from plans, and generate accurate estimates for construction projects. The course will cover various civil works […]
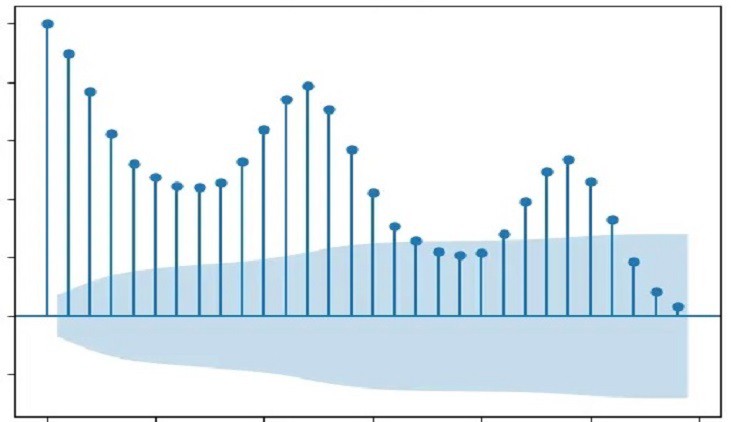
Uniform modeling (i.e. models from a diverse set of libraries, including scikit-learn, statsmodels, and tensorflow), reporting, and data visualizations are offered through the Scalecast interfaces. Data storage and processing then becomes easy as all applicable data, predictions, and many derived metrics are contained in a few objects with much customization available through different modules. The […]
Mobile apps are the next big thing in the world of software. As the number of smart devices continues to increase, likely, the number of mobile applications will also continue to grow. While the latest innovations in mobile devices have made many tasks quicker and easier, there’s no denying that the security of these problem-solving […]
Phone hacking involves any method where someone forces access into your phone or its communications. This can range from advanced security breaches to simply listening in on unsecured internet connections. It can also involve physical theft of your phone and forcibly hacking into it via methods like brute force. It generally means the access of […]
Metasploit is one of the best Hacking operating system. Black Hat hackers and Ethical Hackers use that operating system for hacking computer systems. In this course you will learn and understand how to use Metasploit so that you can computer systems just like Black Hat Hackers and also protect against hacking attacks. First of all […]
Hello and welcome to this course. web developers make a competitive salary compared to other industries. The high earning potential often piques the interest of many computer science prospective students, but the creativity and growth potential are what really seals the deal for most. Consider the Pros It’s always important to consider the pros and […]
Node.js is an open source, cross-platform runtime environment for developing server-side and networking applications. Node.js applications are written in JavaScript, and can be run within the Node.js runtime on OS X, Microsoft Windows, and Linux. Node.js also provides a rich library of various JavaScript modules which simplifies the development of web applications using Node.js to […]
Welcome to the Masterclass of Cultural Clothing Design and Drawing from Around the World, an in-depth and comprehensive course that immerses you in the diverse world of clothing in different cultures using simplified methods. This course allows you not only to explore and analyze traditional clothing styles from 15 distinct cultures worldwide but also to learn how to observe, simplify, […]